
ra2 studio - Fotolia
How to configure Remote Desktop in Windows Server 2008 R2 step by step
Learn how to install and configure Remote Desktop Services on Windows Server 2008 R2 to use Terminal Services and Remote Desktop Gateway Manager.
Microsoft's Remote Desktop Services Virtual Desktop Infrastructure product offers a lot of benefits, but not every IT administrator knows where to start.
As a virtual desktop administrator, you should learn the ins and outs of this VDI product to make the most of it. Learn step by step how to get Remote Desktop Services (RDS) and some of the basic RDS components up and running.
Step 1: Begin the installation
Launch Server Manager and select Server Roles. Once the roles manager screen is up, check the box for Remote Desktop Services. Some other boxes may already be checked, but this is fine -- the only box you need to worry about for this step is the Remote Desktop Services box. Click the next button in the bottom right corner to proceed.
Now you should see an introduction to RDS. Select the next button at the bottom of the page.
Step 2: Select Remote Desktop Services roles you want to install
RDS includes several components and settings (Figure 1). These components can be on one machine or many.
- Remote Desktop Session Host. This is the name for Terminal Server.
- Remote Desktop Virtualization Host. This component integrates with Microsoft Client Hyper-V. This allows for the pooling of virtual machines on Hyper-V so they can serve as virtual desktops.
- Remote Desktop Connection Broker. This component bridges the user with a virtual Windows desktop, remote application or Remote Desktop Session Host session.
- Remote Desktop Licensing. This is the modern name of Terminal Server licensing server that also includes licensing for Windows Server.
- Remote Desktop Gateway. This provides a single connection point for clients to connect to a specific virtual desktop, remote app or Remote Desktop Session Host session.
- Remote Desktop Web Access. This provides clients an interface to access their virtual desktop, remote app or Remote Desktop Session Host sessions.
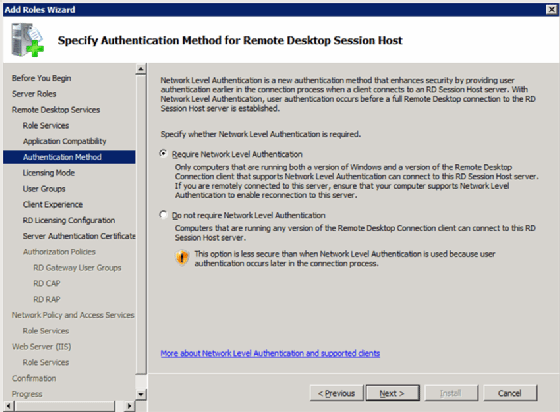
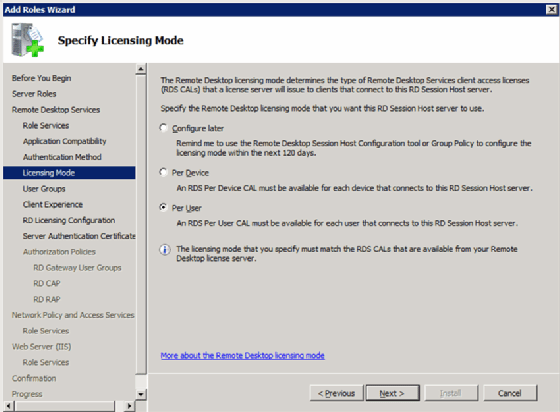
Step 3: Pick the license mode
As with past Terminal Server licensing, there are two license options: per-device and per-user (Figure 2).
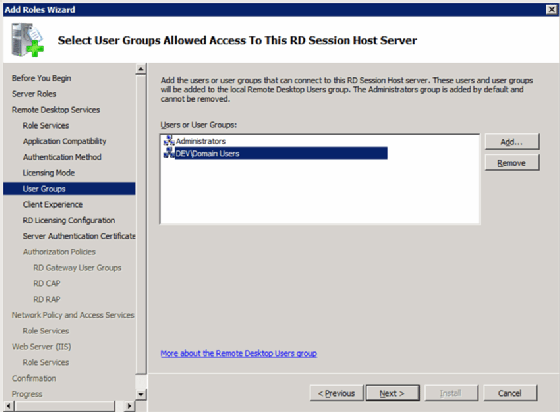
Step 4: Allow access to Remote Desktop Session Host (not required)
Select which users to grant access to the local Remote Desktop Session Host. This server component is not required for RDS to work. If you choose to install the Remote Desktop Session Host, you will get this prompt (Figure 3).
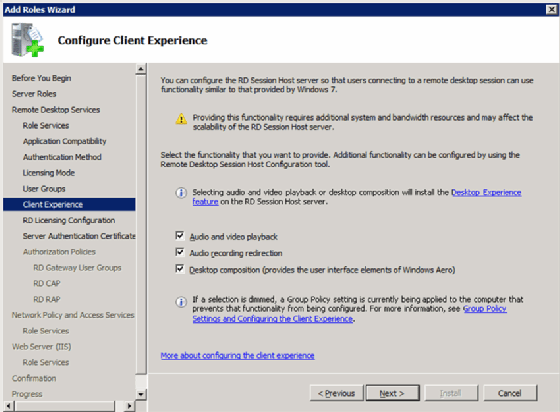
Step 5: Configure the client experience
The next screen is called Configure Client Experience (Figure 4). This is where you set the defaults for the end-user experience with the VDI system and remote desktop.
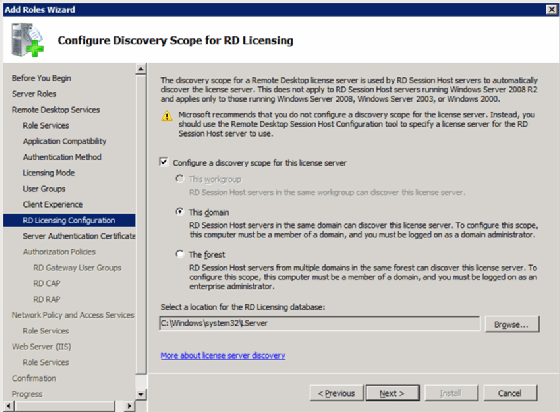
Step 6: Configure license scope
Just as with Terminal Server of the past, you can configure the scope of the Remote Desktop Session Host license server. You have the following two options:
- Domain. This limits the licensing to only servers in the domain (Figure 5).
- Active Directory Forest. This allows any Remote Desktop Session Host server in the Active Directory Forest -- the highest-level container in a set of servers -- to attain a license.
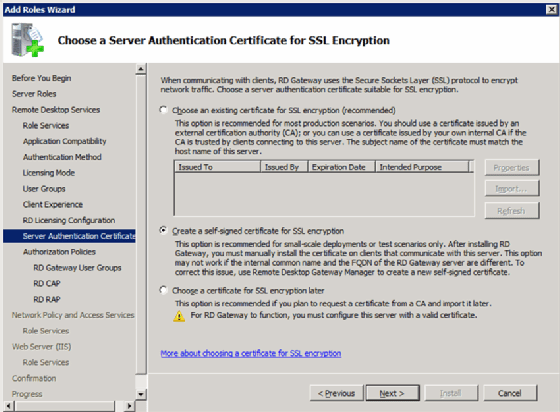
Step 7: Assigning the SSL certificate for Remote Desktop Gateway
The Remote Desktop Gateway uses Secure Sockets Layer (SSL) to tunnel and encrypt traffic from the client. This functionality requires a certificate. There are two options for certificates:
- Specify a certificate from the certificate store.
- Produce a self-signed certificate.
In either case, the client must trust the certificate (Figure 6).
Step 8: Configure network access protection (optional)
These next few screens go beyond the scope of RDS but are related, so this article will just cover the basics.
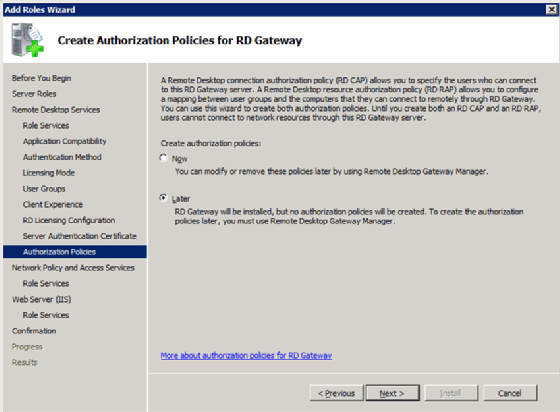
Create authorization policies
This is where you would configure a policy that states who is allowed to establish a desktop connection to the Remote Desktop Gateway
(Figure 7).
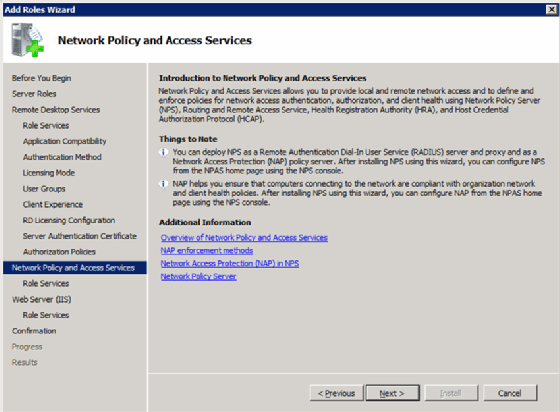
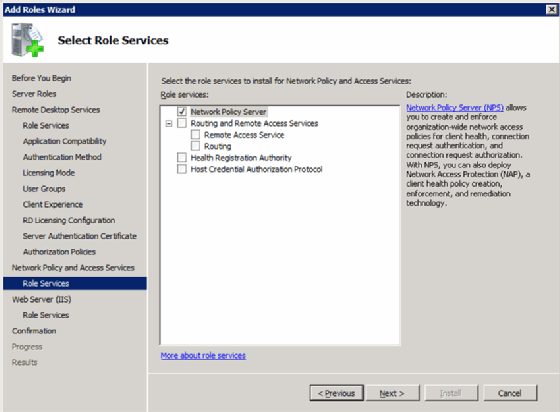
Install and configure network access and protection policies
You can use this to configure and enforce network access policies such as Internet Protocol Security (IPsec) and network access protection from the client (Figure 8).
You can also use this feature to define different policies based on users' connectivity (Figure 9).
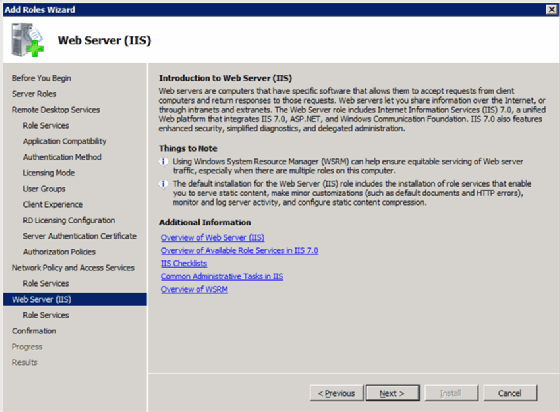
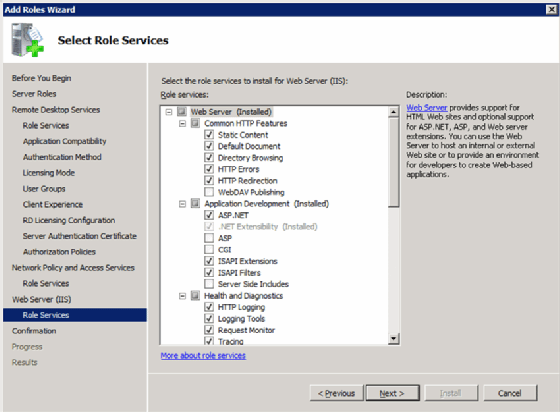
Step 9: Install IIS and Remote Desktop Web Access
Remote Desktop Web Access requires Internet Information Services (IIS), so the next two screens are for installing and configuring IIS. First, there is the overview screen (Figure 10).
The second screen is the configuration screen (Figure 11).
Step 10: The final steps
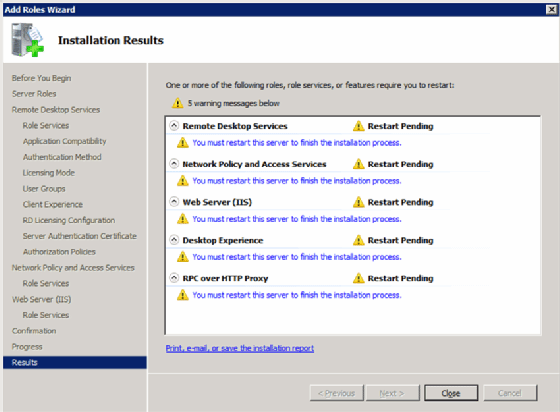
At this point, you're done. The last two screens just let you know what you're installing (Figure 12).
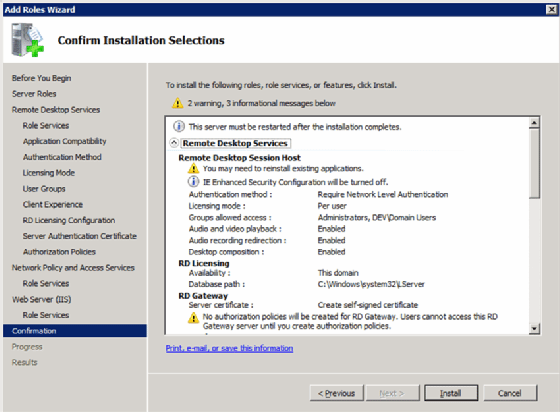
There is also the final screen that lets you know whether any additional steps like rebooting are required (Figure 13).
Now that you have installed and configured RDS, you can start using Remote Desktop Session Host and Remote Desktop Gateway Manager.







